A Step-by-Step Guide to Securing AI Agents with HashiCorp Vault
Overview
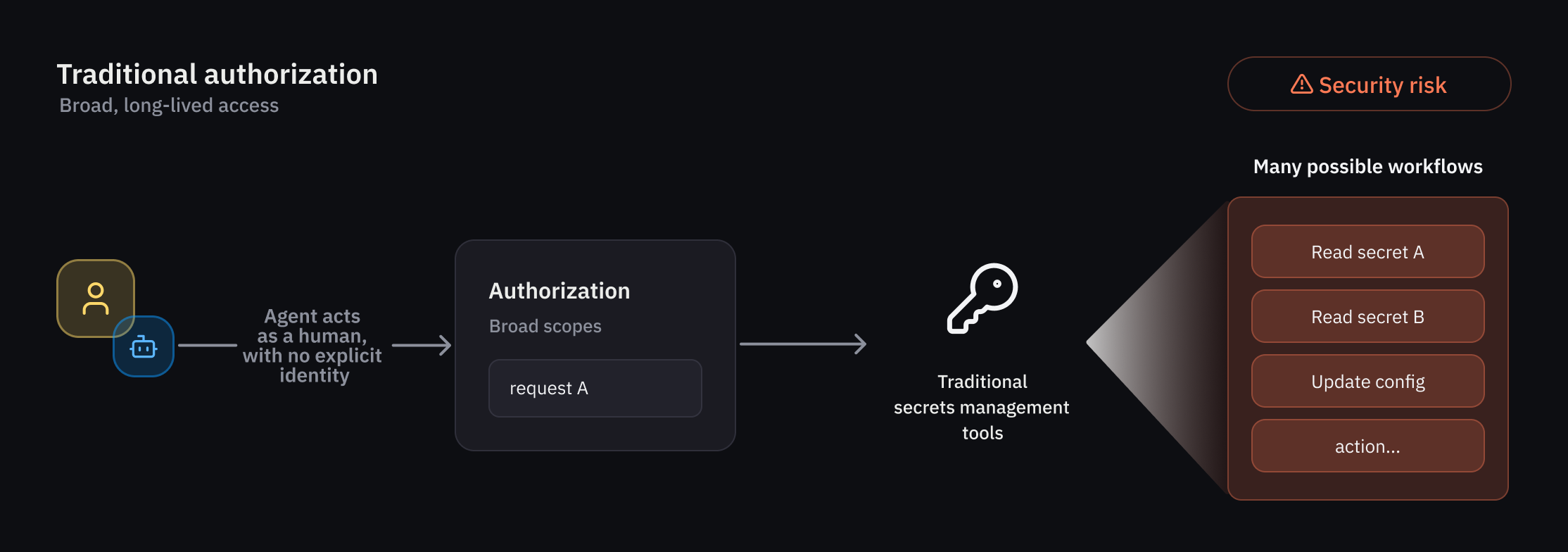
Traditional Identity and Access Management (IAM) was built for predictable, deterministic users and workflows. But AI agents are autonomous, non-deterministic actors that demand a fundamentally different authorization model—one that combines identity, delegation, runtime policy evaluation, and ephemeral permissions. As organizations integrate AI agents into their environments, HashiCorp Vault customers increasingly seek security controls designed specifically for autonomous systems. These include the ability to enforce guardrails for agents that behave less predictably than humans or traditional non-human identities (NHIs), fine-grained authorization that can be evaluated at runtime and scoped to individual actions or workflows, clear attribution and auditability for actions performed on behalf of users, and a standardized approach for securing AI agents across environments.
To meet these needs, HashiCorp introduced new capabilities in Vault for agentic workflows: an agent registry, granular identity-based policies, and per-request (ephemeral) authorization controls. Together, these features reduce risk by granting temporary access rights that expire after a specific task or timeframe. This tutorial will walk you through setting up and using these features, from registering your first AI agent to enforcing least-privilege policies at runtime.
Prerequisites
Before you begin, ensure you have the following:
- HashiCorp Vault – Version 1.18 or later (with the new agent registry feature; check the public beta availability expected summer 2025).
- Vault CLI – Installed and configured with appropriate admin privileges.
- Basic understanding of Vault concepts – policies, authentication methods, secrets engines.
- A sample AI agent – For testing, you can use a simple script that simulates an autonomous agent making API calls to Vault.
- Access to Vault UI (optional) – For visual management of the agent registry.
Step-by-Step Instructions
1. Enable the Agent Registry
The agent registry is the starting point—a dedicated database within Vault that stores agent identities separately from human and NHI identities. To enable it, run:
vault secrets enable -path=agent-registry agentThis mounts the agent registry at the path agent-registry. Verify it's working with:
vault list agent-registry/agents2. Register an AI Agent
Now register a new agent identity. Each agent gets a unique name and associated metadata (e.g., owner, purpose, allowed actions):
vault write agent-registry/agents/my-agent \
owner="data-science-team" \
purpose="automated-data-enrichment" \
allowed_actions="read,write" \
ttl="1h"The ttl field sets the default token lifetime for this agent (ephemeral). You can also specify delegate permissions if the agent acts on behalf of a human user (on-behalf-of pattern).
3. Create an Identity-Based Policy for the Agent
Policies in Vault determine what an authenticated entity can do. For agents, we use deterministic guardrails—rules that are evaluated at runtime, even though the agent's behavior is non-deterministic. Create a policy file named agent-policy.hcl:
path "secret/data/my-app/*" {
capabilities = ["read"]
allowed_parameters = {
"data" = []
}
condition {
source_role = "agent_role"
}
}
path "sys/leases/lookup/*" {
capabilities = ["list"]
}Apply this policy to the agent's role:
vault policy write agent-policy agent-policy.hcl
vault write auth/agent-role/role/my-agent policies="agent-policy"Notice we use condition blocks—these allow runtime evaluation of attributes like the delegation context (e.g., the human user who delegated authority).
4. Configure Ephemeral Authorization
Ephemeral authorization is the key to reducing risk. It grants temporary access that expires after a single task or a short timeframe. When the agent requests a token, we set a short TTL and limit the number of uses:
vault token create -policy=agent-policy \
-ttl=10m \
-use-limit=5 \
-display-name="my-agent-task"Alternatively, if the agent is using the on-behalf-of flow, the delegated user can generate a token with ephemeral constraints:
vault write auth/agent-role/login role=my-agent \
delegation_token=$(vault token create -ttl=5m -use-limit=1 -format=json | jq -r '.auth.client_token')5. Test the Agent Authentication
Simulate your agent authenticating to Vault using the registered identity. For example, using a client that supports the agent-auth method:
export VAULT_TOKEN=$(vault login -method=agent \
-path=agent-registry/auth/my-agent \
-token-only=true)Then attempt to access a secret:
vault kv get secret/data/my-app/passwordYou should see the data if the policy allows. Try exceeding the use-limit or TTL—the request will be denied.
6. Set Up Auditing and Observability
Every action an agent performs is logged. Enable audit logs (if not already) and tail them:
vault audit enable file file_path=/var/log/vault-audit.log
sudo tail -f /var/log/vault-audit.log | grep "agent-registry"In the logs, you'll see the agent's identity (name, role) and the delegated user (if any). This provides clear attribution for compliance.
Common Mistakes
- Not setting a TTL or use-limit – Agents may accumulate long-lived tokens, defeating the purpose of ephemeral authorization. Always enforce tight time and usage constraints.
- Overly permissive policies – Because agents are non-deterministic, a broad policy like
path "*" { capabilities = ["*"] }is catastrophic. Useconditionblocks and scoped paths. - Mixing human and agent identities – The agent registry is separate for a reason. Avoid registering agents under human user paths—use the dedicated agent engine.
- Forgetting to enable delegation tracking – If your agent acts on behalf of a human, make sure the
delegation_tokenis passed and logged. Otherwise, you lose audit trail. - Ignoring policy evaluation order – Vault resolves policies in alphabetical order. Test with a deny-first approach to avoid accidental access.
Summary
Securing AI agents with HashiCorp Vault requires a shift from static IAM to a dynamic, identity-based, ephemeral authorization model. By leveraging the new agent registry, you can separate agent identities from humans, enforce granular policies with runtime conditions, and grant temporary tokens that expire after a single task. This guide covered registering an agent, creating a policy, configuring ephemeral tokens, and auditing agent actions. With these steps, you can safely integrate autonomous AI into your infrastructure while maintaining least-privilege and full accountability.
Related Articles
- Design Principles: A Team's Compass for Better Decision-Making
- Escaping the AI Hype: 6 Questions About Free, No-Frills Productivity Apps
- North Korea-Linked Hackers Hijack Axios JavaScript Library in Sophisticated Supply Chain Attack
- Mastering GitHub Copilot CLI: A Step-by-Step Guide to Interactive and Non-Interactive Modes
- April 2026 Linux Application Updates: Kdenlive, VirtualBox, Firefox, and More
- How to Transform Defense Innovation: Lessons from Anduril and CEO Brian Schimpf
- Why I Ditched OneDrive for Ente Photos: A Privacy-Focused Photo Storage Switch
- How to Avoid Passport Revocation: A Guide to the New Child Support Enforcement Policy