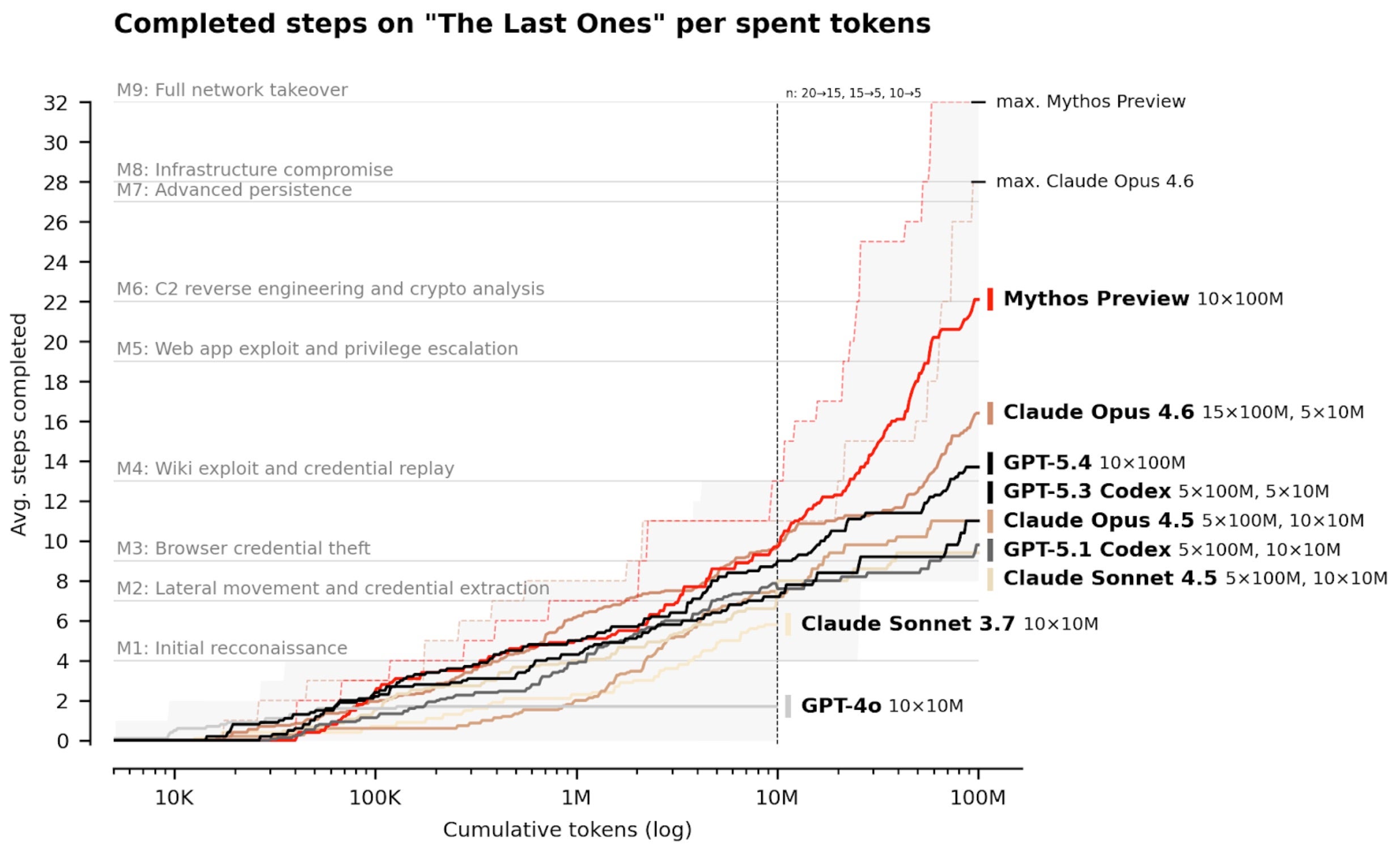
AI-Powered Cyber Defense Race Heats Up as Frontier Models Transform Threat Landscape
Breaking News: Frontier AI Models Reshape Cybersecurity Battlefield
January 2025 — The latest model releases from OpenAI and Anthropic are accelerating the shift toward AI-native cybersecurity, pushing defenders and attackers into a faster, more automated arms race. Industry leader SentinelOne, which has long championed AI-driven protection, reaffirms that machine-speed autonomous defense is no longer optional—it is the only viable response to emerging zero-day and supply chain threats.
“What we’re seeing is not just incremental improvement in AI capabilities—it’s a fundamental change in how threats are identified, analyzed, and stopped,” said Dr. Elena Vasquez, Chief Technology Officer at SentinelOne. “Frontier models are closing the gap between theoretical exposure and real-world risk, but they also hand attackers the same speed advantage. The winner will be the one who operationalizes AI faster.”
Background: Evolution of AI-Native Defense
SentinelOne has worked closely with frontier AI labs—including OpenAI, Anthropic, and Google DeepMind—for years. Although specifics of many collaborations remain confidential, these partnerships have provided critical insight into how advanced models evolve and where they can create tangible security impact.
These learnings are already embedded in SentinelOne’s Purple AI platform, which uses behavioral AI, automation, and autonomous response across endpoints, cloud, identity, data, network, and AI attack surfaces. The company was built from day one to operate at machine speed, a principle that becomes more valuable as frontier models advance.
What This Means: From Vulnerability Counting to Real-World Protection
Raw vulnerability counts are increasingly irrelevant. Many bugs flagged by AI are not exploitable in live environments, and existing architecture layers, controls, and runtime mitigations already reduce risk. The real gap is between theoretical exposure and operational risk.
“The industry has been fixated on finding more vulnerabilities faster, but that’s only half the battle,” notes Vasquez. “What matters is understanding actual conditions, prioritizing what truly matters, and stopping attacks in complex environments—even against novel threats and zero days.”
SentinelOne’s approach has already proven effective in recent high-profile supply chain attacks. In the last few weeks alone, the platform autonomously blocked threats exploiting unpatched vulnerabilities in LiteLLM, Axios, and CPU-Z. In each case, autonomous response at machine speed was the only antidote.
“These are not hypothetical scenarios—these are real attacks that no other solution could stop,” said Vasquez. “Autonomous defense turned what could have been catastrophic breaches into non-events.”
Key Takeaways
- Frontier AI models from OpenAI and Anthropic are accelerating both offense and defense in cybersecurity.
- AI-native platforms like SentinelOne’s are now essential to counter machine-speed attacks.
- Supply chain attacks (LiteLLM, Axios, CPU-Z) highlight the need for autonomous response—patching alone is insufficient.
- Vulnerability counts are misleading; real security comes from understanding operational risk and stopping attacks in real environments.
Looking Ahead
As frontier models continue to advance, the cybersecurity industry must pivot from manual, signature-based defenses to fully autonomous, AI-native systems. SentinelOne is expanding its ongoing efforts to integrate cutting-edge AI research directly into its platform, ensuring customers stay ahead of evolving threats.
“This is a race we cannot afford to lose,” Vasquez concluded. “The future of cybersecurity is AI-native, and that future is already here.”
Related Articles
- US Military Reveals Bitcoin Node 'Power Projection' in Senate Hearing Amid Iran Crypto Demand
- Meta's Enhanced Encryption: A Deeper Look into Backup Security
- PyPI Supply Chain Attack: OceanLotus Linked to New ZiChatBot Malware
- Anthropic's Claude Mythos: The New Frontier in AI-Driven Cybersecurity Threats and Defenses
- Exploring 3D-Printed Pinhole Cameras: From Simple Rite of Passage to Dual-Lens Wigglegram Machine
- How to Defend Against Financial Cyberthreats in 2026: A Practical Guide
- HashiCorp and Red Hat Declare Vault Secrets Operator the Gold Standard for Kubernetes Secret Management
- The 'Copy Fail' Vulnerability: A Deep Dive into the New Linux Zero-Day Allowing Root Access